
Secure,
Open &
Verifiable
silicon foundations for the digital world
Today, confidential computing means dependence on suppliers, hyperscalars and security-through-obscurity.
We are building Project Sovereign, a physically secure, radically open chip to replace trust and dependence with technical auditability.


We are a public goods R&D project. Our aim is to build silicon that embodies our principles of verifiability and openness in the real world, and to share the designs and lessons for others to go further in that mission.
We are presently in an exploration phase, building a clear understanding of the security, cost and performance tradeoffs that we face, and the wide space of secure hardware use cases - from AI & crypto to robotics & biometrics.
FAQ
-
Project Sovereign is stewards by the Trustless TEE team: ml_sudo and Quintus Kilbourn, and was initiated by Flashbots.
Our role is to be the glue between the various people who hold pieces of our puzzle. This includes various security researchers, engineering teams, funders and users.
-
We are presently in an exploration phase, building a clear understanding of the security, cost and performance tradeoffs that we face, and the wide space of secure hardware use cases - from AI & crypto to robotics & biometrics.
We are fundraising to enable a technical study of these tradeoffs, involving implementation of several components, and to initiate work on the most critical security primitives: PUF-based keys and the cryptographic circuits surrounding them,
-
The Trustless TEE project operates under the administration of the PBS Foundation.
It is not a for-profit project. Funds raised are considered donations.
-
We see secure hardware as a powerful complement to MPC and other forms of programmable crypto. For instance, TEEs can help to protect MPC schemes against collusion attacks.
In other cases, TEEs are provide a low-overhead alternative to unprotected computation when cryptographic schemes and distributed systems are simply too slow or expensive. For example, TEE+ORAM based private information retrieval schemes are already implemented in several production settings (e.g. Signal contact discovery), and TEE-based block building is being used in blockchains like Ethereum and Solana.
Systems based heavily on digital signatures such as blockchains, are often serviced by key management systems such as wallets-as-a-service. Many of these constructions rely on TEEs to protect threshold secrets. -
At a high level, there are five ways in which we are relevant:
We plan to be able to run high security models, providing confidential inference, model weight protections, and verifiable policy enforcement.
AI safety work such as the FlexHEG line of work, utilise the idea of highly trustworthy “guarantee processors” that sit next to powerful AI hardware for frontier models.
Outside of the models themselves, the agentic world increases the need for security and privacy tools, to protect systems from attack and to facilitate coordination between agents.
In a world where synthetic data is cheap to generate and impossible to detect, data provenance is extremely important. C2PA standards are one example. Biometric proof-of-humanity systems are another.
Along with the rise of AI, we are seeing more and smarter robotics being deployed to sensitive areas. Having technical assurances that data collected by these machines is not being sent to unexpected places is essential for privacy.
-
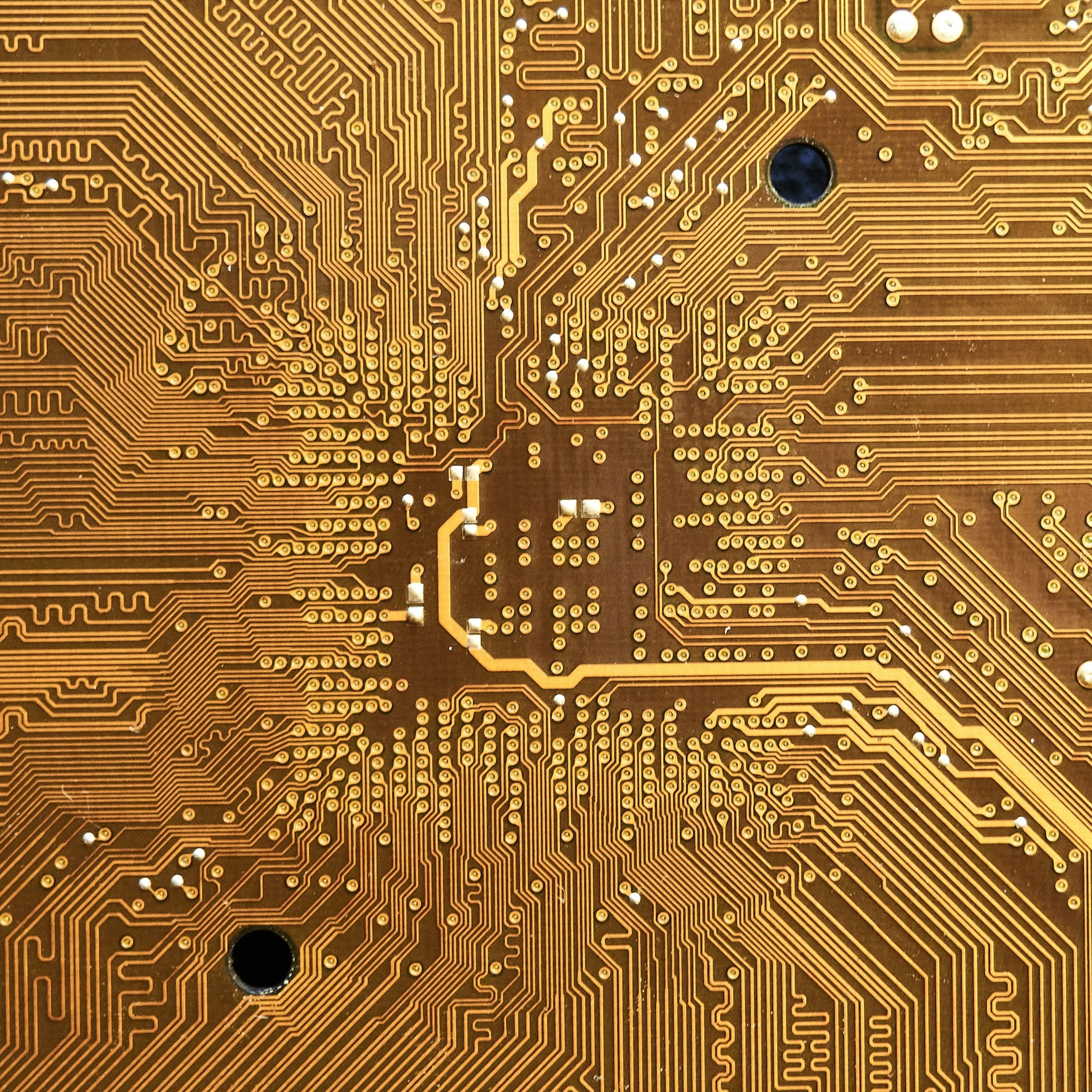
We want to taken open hardware further than it has gone before.
Open hardware is a complex topic. In the ideal case, everything required to verify and replicate designs is publicly available. In practice, many layers of legal agreements make it very hard for most projects to publicise meaningful details.
Today, almost all hardware and the low-level software that accompanies it is completely opaque. Some open hardware projects have trailblazed a path by opening logical descriptions of their components. On some old technologies (90+nm), people have gone further to full openness.We aim to publicise physical details (LIB/LEB/DEF files) in addition to logical descriptions. We are able to do this through possession of a custom cell library. This is unprecedented for silicon anywhere near the sophistication we are targeting (12nm).